Contact Stream Start 717-205-1303 Revealing Phone Trace Insights
The discussion centers on Contact Stream Start 717-205-1303 and the resulting phone trace insights. It presents how trace data identifies the initiator, routes signals, and aggregates timing and network path details. The approach emphasizes corroborating origins, detecting anomalies, and assessing credibility with minimal exposure of sensitive data. The framework asks readers to consider verification methods and potential masking strategies, leaving open questions about reliability and practical application that warrant further examination.
What Phone Trace Data Reveals About Callers
Phone trace data provides a precise snapshot of who initiates calls, revealing patterns in dialing behavior, geographic origin, and network routing. The data clarify caller behavior, exposing anomalies and consistency across sessions. Findings emphasize caller ID deception as a potential masking strategy, while call origin tracing highlights verifiable routes. Conclusions support informed freedom through transparent investigation and evidence-based policy guidance.
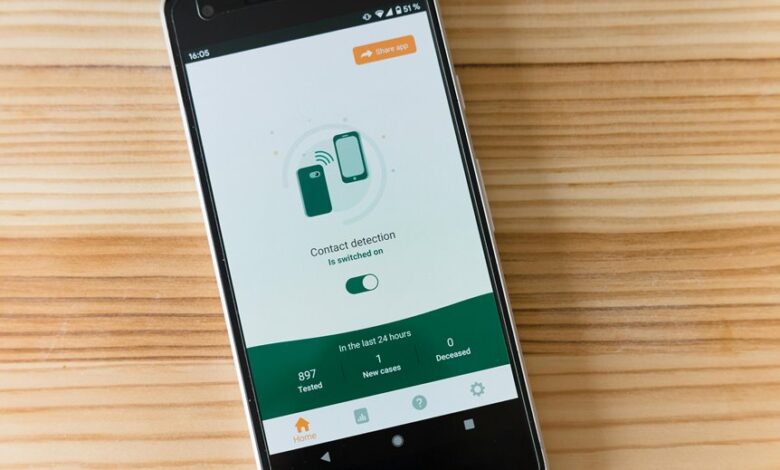
How Contact Stream Trace Works: A Quick Primer
Contact Stream tracing operates by aligning call metadata with network path information to reveal the sequence of events that deliver a connection.
The method aggregates timing, routing, and signaling data to map how a call propagates through infrastructure.
This quick primer clarifies how contact stream reduces ambiguity, enabling disciplined verification without revealing sensitive personal details.
contact stream informs, not intrudes.
Spotting Red Flags and Verifying Caller Credibility
Spotting red flags and verifying caller credibility require a systematic approach grounded in objective indicators rather than impression. The analysis assesses caller provenance, verification of claimed affiliations, and consistency of metadata with known patterns. Indicators include incongruent time zones, inconsistent caller IDs, and unusual solicitation tactics. Related signals, such as unrelated topic contexts and offbeat angles, inform skepticism without conflating risk with novelty.
Practical Steps to Analyze Patterns and Protect Yourself
With an established framework for evaluating caller credibility, practical steps focus on pattern analysis and protective actions. Systematic data collection tracks caller patterns across attempts, times, and durations, enabling anomaly detection and trend mapping.
Verification relies on cross-referencing publicly available records and reported behaviors. Implement risk-minimizing responses, privacy safeguards, and escalation protocols to reinforce caller credibility while preserving personal freedom. Continuous review maintains resilience.
Conclusion
In the hush of data logs, the contact stream unfolds like a mapped river: each ripple marks a dialed number, each current shift hints at origin and path. The trace, when aligned with network routing, reveals a disciplined sequence that separates credible signals from noise. As patterns emerge—timing, hops, anomalies—verification sharpens, casting light on potential masking. The result is an evidence-based portrait of credibility, drawn with precise metrics and measured inference.





