Contact Vision Start 623-352-9402 Revealing Phone Trace Discovery
Contact Vision Start 623-352-9402 reveals a methodical approach to phone trace discovery, focusing on how metadata and logs can map call origins and message paths. The discussion balances data minimization, transparency, and verification, while questioning limitations and privacy bounds. It invites scrutiny of tracing tools, consent boundaries, and real-world applicability, prompting readers to consider how evidence-based methods stand up under scrutiny, and what steps must follow before conclusions emerge. The next detail awaits.
What Is Phone Trace Discovery and Why It Matters
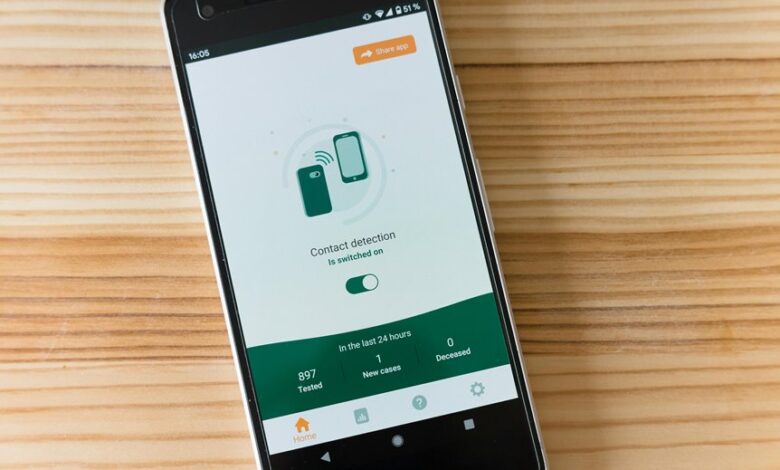
Phone trace discovery refers to the process of identifying the origin of a call or message by analyzing telecommunications data and network traces. It is examined with methodical precision, probing capabilities and limits, to reveal patterns without compromising fundamental rights.
The topic weighs benefits against risks, emphasizing caller privacy while highlighting legitimate safety uses, data governance, and accountable practices in investigative contexts.
How Tracing Tools Work: Data, Limits, and Privacy
How do tracing tools translate raw telecom data into actionable insight without overstepping privacy boundaries? They convert metadata, call logs, and network signals into patterns, estimates, and timelines, while applying strict access controls and minimization.
Tracing tools basics emphasize transparency and auditability. Privacy considerations foreground data scope, retention, and consent, ensuring trust without compromising investigative value.
Verifying Unknown Callers: Steps and Best Practices
Unknown calls pose a persistent challenge for informed decision-making, inviting a methodical approach to verification rather than reflexive caution. Verifying unknown callers demands structured steps: confirm context, avoid assumptions, and employ tracing tools judiciously. Assess reliability of data, cross-check with independent sources, and document findings. Curiosity should drive caution, preserving freedom while reducing misidentification risks from unknown callers.
Legal, Security, and Practical Considerations for The Real World
For the Real World, navigating legal, security, and practical considerations requires a disciplined, evidence-driven approach: what rights, obligations, and safeguards apply when investigating or responding to suspected traces, and how do these intersect with everyday decision-making?
The inquiry scrutinizes privacy concerns and data accuracy, highlighting proportionality, consent boundaries, and verification. A critical, curious stance seeks transparent protocols and accountable practices for informed, freedom-respecting action.
Conclusion
The study closes with a curious, methodical shrug at the glittering promise of “phone trace” as a silver bullet. In a landscape of data-minimization and consent, one suspects tracing tools are less a Panacea and more a laboratory experiment—clever, noisy, and dangerously optimistic. Yet the critique is pointed: without transparent governance, independent verification, and proportionality, even the most precise traces resemble garden gnomes—visible, entertaining, but fundamentally inadequate for real-world decisions. Satire aside, accountability remains indispensable.





