Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
The text outlines an account data review framework centered on governance, accuracy, and traceability across systems. It emphasizes identity and access governance, disciplined log reconciliation, and risk-based control prioritization. The approach aligns policies, entitlement modeling, and threat assessment to minimize friction while maintaining accountability and resilience. This alignment promises robust data protection and transparent governance, yet the practical implications for daily operations remain complex and open to interpretation. The next step is to evaluate how these elements integrate in real-world environments.
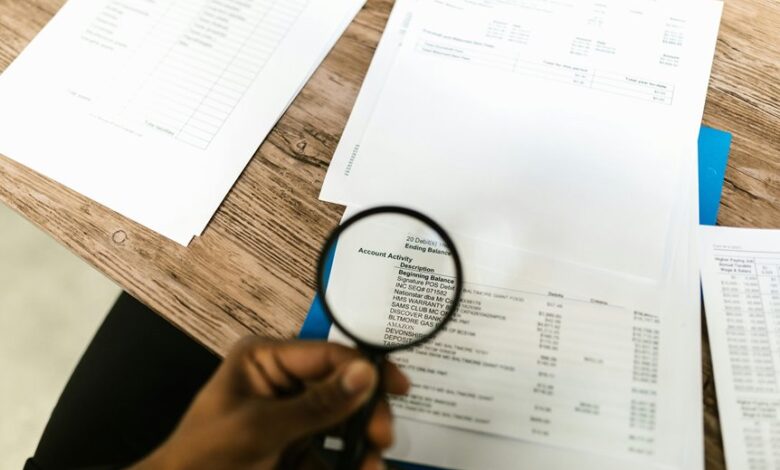
What Is Account Data Review and Why It Matters
Account data review is a systematic process of examining the inputs, storage, and usage of user and system data to verify accuracy, consistency, and compliance. It clarifies governance boundaries and supports accountability. The analysis emphasizes Account verification and Data integrity, ensuring traceability, flagging anomalies, and sustaining trusted operations. This framework fosters disciplined decision-making while respecting user autonomy and system resilience.
How to Validate Identities and Access Across Systems
Validating identities and access across systems requires a structured approach that identifies who is authorized to act, what resources they may access, and under what conditions such access is granted.
The analysis emphasizes data integrity and access governance, aligning identity verification with policy, entitlement modeling, and risk assessment.
This methodical process enhances interoperability, minimizes risk, and preserves user freedom through transparent controls.
Reconciling Activity Logs to Spot Anomalies
Reconciling activity logs to spot anomalies entails a disciplined, data-driven examination of event sequences across systems to identify deviations from established baselines.
The process emphasizes Access management, data integrity, and threat modeling as core pillars, with systematic reviews feeding risk assessment.
Through structured comparisons, inconsistencies reveal potential compromise, policy breaches, or misconfigurations, enabling timely containment and robust, freedom-aligned governance.
Prioritizing Risks and Enforcing Simple Controls
How should an organization distill a broad risk landscape into actionable priorities and simple, enforceable controls?
The analysis selects high-impact threats via threat modeling, then aligns controls with data governance objectives.
Prioritization follows likelihood and impact, balancing risk appetite with practicality.
Implementations emphasize minimal friction, traceability, and continuous review, ensuring governance, transparency, and measurable security improvements across systems and processes.
Frequently Asked Questions
How Often Should Account Data Reviews Be Conducted for This ID Set?
The account review cadence should be quarterly for this id set, with ongoing monitoring. If risk indicators escalate, increase frequency to monthly; if indicators remain stable, consider semiannual checks while maintaining documented thresholds and audit-ready processes.
What Metrics Indicate Resources Are at Risk During Review?
An initial 37% drop in transfer latency signals resource strain. In reviews, metrics include data minimization adherence and risk signaling thresholds, with systematic drift indicating aging resources; precise, analytical evaluation ensures safe freedom through disciplined governance.
Can Data Reviews Impact User Access Timelines or SLAS?
Data reviews can influence access provisioning timelines and SLAs, as audits affect approvals and remediation efforts; data quality issues may delay permissions, while streamlined processes preserve objectives for timely access despite governance controls.
Which Tools Best Integrate With Existing Identity Platforms?
Integration governance and identity automation favor platforms offering broad API comfort, extensible connectors, and lifecycle orchestration. Analytical evaluation suggests selecting tools with standards-based adapters, documented workflows, and rigorous access control to empower enterprise freedom within integrated identity ecosystems.
How Is Compliance With Data Retention Policies Verified?
A hypothetical financial institute demonstrates compliance verification by auditing data retention schedules, validating automated retention tags, and sampling logs; this reveals that retention policy alignment is maintained through quarterly reviews, policy mapping, and cross-functional attestations.
Conclusion
In the end, the framework tests itself against doubt. Each identity, each entitlement, every log line becomes a measured pulse—a signpost in the night. The methodical reconciliation reveals gaps with chilling certainty, while risk-prioritized controls promise frictionless protection without stifling autonomy. As anomalies tighten the narrative, decisions emerge with unsettling clarity: governance is not a verdict but a vigilant cadence. The data remains under watch, and the quiet, persistent cadence hints at a deeper accountability.





