Account Data Review – 8888708842, 3317586838, 3519371931, Dtyrjy, 3792753351
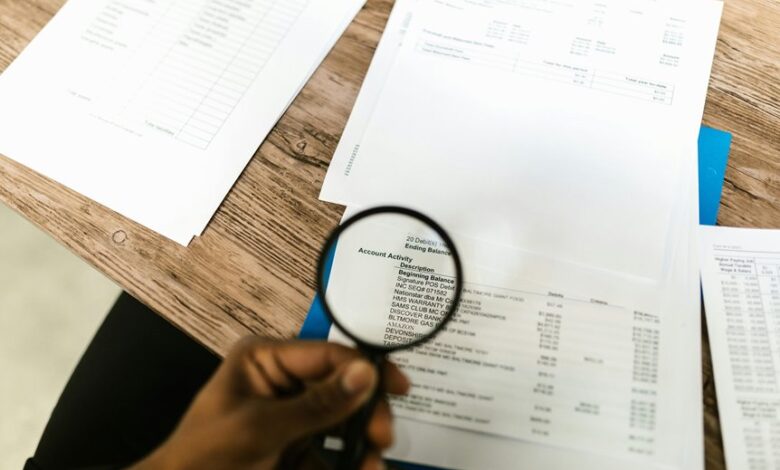
The account data review for 8888708842, 3317586838, 3519371931, Dtyrjy, and 3792753351 applies a metric-driven framework to identify gaps and inconsistencies in data. Baseline metrics measure completeness, timeliness, and error frequencies across accounts, while patterns and anomalies are monitored to surface privilege gaps and unusual activity. The approach supports proactive remediation and transparent governance, yet it leaves unresolved questions that demand careful evaluation before implementation conclusions can be drawn.
What the Account Data Review Aims to Solve
The Account Data Review aims to identify gaps, inconsistencies, and risks within the account data, ensuring accuracy, completeness, and reliability for decision-making. It focuses on uncovering data defects, aligning sources, and validating records to support trusted outcomes.
Account data review aims to solve data integrity challenges by standardizing inputs, verifying transformations, and sustaining transparent, auditable data governance for stakeholders seeking freedom through clarity.
Baseline Metrics for 8888708842, 3317586838, 3519371931, 3792753351, and Dtyrjy
Baseline metrics for the listed accounts—8888708842, 3317586838, 3519371931, 3792753351, and Dtyrjy—establish key performance and integrity indicators, including completeness rates, data timeliness, transformation accuracy, and error frequencies, to support objective assessment and governance.
The metrics illuminate security gaps, anomaly patterns, and governance playbook alignment, guiding proactive corrective actions while preserving freedom to operate efficiently within compliance boundaries.
Identifying Patterns, Anomalies, and Security Gaps
What patterns emerge from cross-account data activity, and where do anomalies and security gaps concentrate across 8888708842, 3317586838, 3519371931, 3792753351, and Dtyrjy?
The data review reveals recurring access peaks, unusual timing, and cross-linking events signaling anomalies.
Identifying patterns clarifies risk areas; security gaps appear in authentication, privilege propagation, and monitoring blind spots.
Continuous review mitigates exposures without sacrificing user freedom.
Practical Audit and Monitoring Playbook for Ongoing Governance
A practical audit and monitoring playbook for ongoing governance defines a repeatable, risk-focused approach to data access and activity across accounts 8888708842, 3317586838, 3519371931, 3792753351, and Dtyrjy. It emphasizes continuous monitoring, documented roles, and access reviews, addressing security gaps and governance gaps.
The framework supports proactive remediation, metric-driven improvements, and transparent reporting while preserving freedom to operate within compliant boundaries.
Frequently Asked Questions
How Is Data Anonymization Handled Across the Accounts?
Data anonymization is achieved through data masking and strictly enforced access controls. Across the accounts, sensitive fields are obscured, and permissions are minimized to essential roles, ensuring auditors can verify integrity without exposing identifiable information or compromising privacy.
What Are the Fallback Procedures for False Positives?
Why assume accuracy when false positives occur, and how are remediation steps defined? The system implements predefined remediation steps for false positives, documenting escalation paths, review windows, and rollback options to minimize disruption and preserve data integrity.
Who Approves Changes to Baseline Metrics and Dashboards?
Changes to baseline metrics and dashboards are approved by designated data governance authorities through formal change approvals, ensuring proper data lineage and access controls are preserved while maintaining transparent, auditable collaboration that supports an audience seeking freedom.
How Frequently Are Third-Party Data Sources Audited?
Third person: Third-party data sources are audited on a quarterly basis, ensuring data governance standards and data lineage integrity are maintained. Audits verify source reliability, documentation, and compliance, supporting transparent, compliant decision-making with ongoing risk assessment and remediation.
What Remediation Steps Follow a Detected Data Breach?
What remediation steps follow a detected breach, and who attends to them? The plan includes remediation steps, data anonymization, fallback procedures, and change approvals, supported by third party audits ensuring transparency while maintaining freedom and compliance.
Conclusion
The Account Data Review consolidates data quality efforts across the five accounts, revealing gaps and strengthening governance. By benchmarking completeness, timeliness, and error frequencies, it exposes patterns, anomalies, and privilege gaps that demand proactive remediation. The approach supports transparent reporting and trusted decision-making. Investigating the theory that standardized inputs and validated transformations reduce risk yields a concise, precise conclusion: rigorous, metric-driven review materially improves data integrity and security posture.





