Account Data Review – PreĺAdac, екфзрги, 18552099549, 8148746286, 3237633355
The discussion on Account Data Review for PreĺAdac, екфзрги, 18552099549, 8148746286, 3237633355 centers on establishing clear objectives, scope, and measurable success criteria. It emphasizes harmonizing multilingual identifiers and encodings, while documenting assumptions and ownership. A disciplined workflow—planning, data selection, evidence gathering, validation, and reporting—will be outlined with checklists and governance constructs. The goal is traceable, auditable results; yet practical gaps and risk considerations suggest that further specifics must be clarified before proceeding.
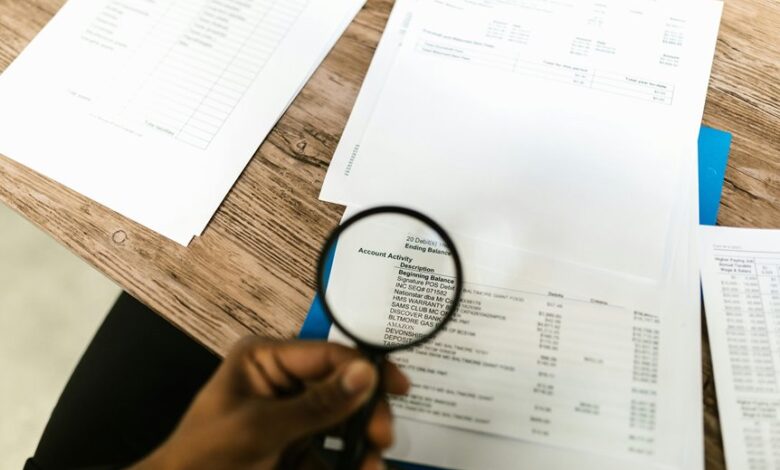
How to Begin an Account Data Review: Core Goals and Clean-Start Steps
A structured approach to initiating an account data review begins with establishing clear objectives, defined scope, and measurable success criteria. The process emphasizes consensus building and rigorous risk assessment to align stakeholders, define controls, and forecast impacts.
A methodical, detail-oriented framework follows standardized steps: inventory data assets, map ownership, set milestones, document assumptions, and ensure traceability, minimizing ambiguity while enabling effective future auditing and improvement.
Verifying Key Identifiers Across Languages and Encodings
Verifying key identifiers across languages and encodings requires a disciplined approach to ensure consistency and reliability. The analysis focuses on preserving semantic equivalence while navigating script variations, normalization forms, and locale-specific rules. Techniques include standardized normalization, explicit encoding contracts, and robust mapping tables. Verifying identifiers benefits from audits, traceability, and cross language encoding validation to prevent misinterpretation and data drift.
Detecting Duplicates, Anomalies, and Inconsistencies in Your Records
Detecting duplicates, anomalies, and inconsistencies in records requires a disciplined, systematic approach to data quality. The analysis focuses on identifying duplicates inconsistencies across sources, employing cross-field comparisons, and validating multilingual identifiers for alignment. Researchers document findings with traceable methods, ensuring reproducibility. Clear thresholds, metadata, and audit trails support accurate decisions, preserving data freedom while maintaining rigorous, objective record integrity.
Practical Workflows and Checklists for Auditing Data Efficiently
How can teams structure audits to maximize consistency and speed without sacrificing accuracy? Pragmatic workflows outline independent phases: planning, data selection, evidence gathering, validation, and reporting.
Checklists enforce discipline, reduce drift, and traceability.
Data governance frameworks codify controls, while risk assessment prioritizes high-impact areas.
Detailing roles, checkpoints, and automation ensures reproducibility, transparency, and efficient collaboration across stakeholders.
Frequently Asked Questions
How Often Should I Run an Account Data Review?
A data review should be conducted regularly, at least quarterly, to monitor data retention, data minimization, compliance drift, and data lineage, ensuring ongoing alignment with policies while preserving freedom to innovate and adapt storage and governance practices.
Which Tools Best Detect Subtle Data Drift?
Data drift is best detected by drift-aware monitoring tools and model-agnostic analyzers that track distribution shifts, feature importance, and lineage. These support privacy governance by documenting changes, thresholds, alerts, and audit trails for compliance-minded reviewers.
Can I Automate Consent Status Checks?
Automating consent status checks is feasible; a system can schedule, track, and log changes. The approach supports Automated consent and Compliance audits, enabling continuous verification, alerting, and documentation while preserving autonomy and governance over data-use practices.
How to Handle Regional Privacy Restrictions?
“Like clockwork” a methodical observer notes that handling regional privacy requires ensuring user consent, data localization, and data minimization, while respecting regional privacy constraints and upholding lawful limits across jurisdictions and compliance processes.
What Are Common Post-Audit Remediation Steps?
Post-audit remediation steps typically include validating findings, prioritizing fixes, and documenting changes; preaudit risk assessments inform scope, while data stewardship ensures accountable ownership, traceable actions, and ongoing monitoring for compliance and freedom to operate.
Conclusion
In sum, the account data review evolves through disciplined planning, meticulous verification of multilingual identifiers, and vigilant detection of duplicates and anomalies. The process emphasizes traceability, ownership, and explicit encoding contracts to minimize drift and support reproducibility. By aligning data inventories with clear milestones and checklists, teams can achieve auditable, language-agnostic integrity. As the final bell tolls, one might imagine a vintage typewriter ding signaling a completed, artifact-like record—an anachronism that underscores precision in a digital age.





