Data Vision Start 689-240-7776 Unlocking Reliable Caller Discovery
Data Vision Start 689-240-7776 proposes a framework for unlocking reliable caller discovery by integrating verifiable signals from networks, devices, and signaling metadata. The approach emphasizes cross-layer validation, scalable processing, and auditable metrics to reduce false positives while preserving privacy. Real-time indicators—latency, precision, recall—are framed as design constraints rather than afterthoughts. The balance between performance and privacy invites careful evaluation of trade-offs, inviting stakeholders to consider implementation implications before proceeding.
What Is Reliable Caller Discovery and Why It Matters
Reliable caller discovery refers to the systematic identification and verification of legitimate incoming calls, using verifiable data signals to distinguish them from spoofed or fraudulent ones.
The approach emphasizes trusted processes, transparent metrics, and scalable validation.
It enables trustworthy mapping of call origins while maintaining privacy safeguards, reducing false positives, and enhancing defender confidence in telecommunications ecosystems.
Freedom-forward design supports auditable, data-driven decision making.
How Data Sources Drive Accurate Caller Identity
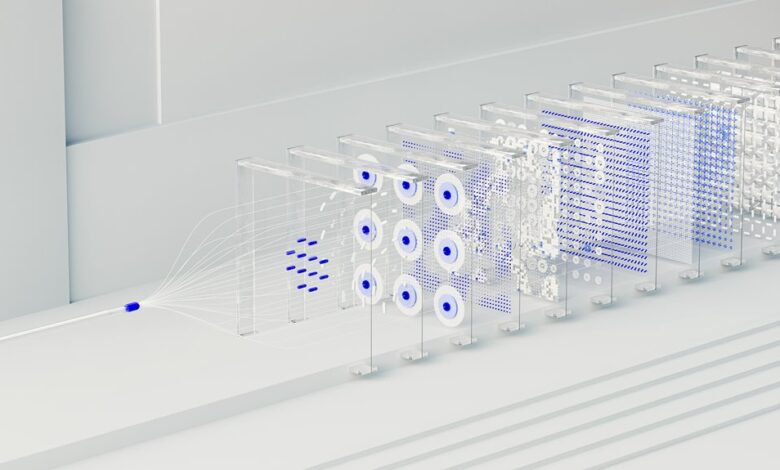
Data sources underpin accurate caller identity by providing verifiable signals that can be cross-validated across multiple layers of the communications stack. In this framework, caller identity emerges from corroborating signals such as originating networks, device fingerprints, and signaling metadata. Data sources enable robust attribution, reducing ambiguity and enhancing reliability without overreliance on any single feed or assumption.
Measuring Quality: Metrics and Validation for Real-Time Discovery
Measuring quality in real-time discovery hinges on defined metrics and rigorous validation to ensure timely, accurate caller identification.
The analysis relies on reliable data, benchmarking against uncertainty metrics, and transparent error budgeting.
Metrics must account for latency, precision, and recall within conversation constraints, while validation uses historical and live streams.
The outcome emphasizes reproducibility, confidence intervals, and disciplined iteration for trustworthy discovery.
Implementing Scalable, Privacy-Safe Caller Discovery in Practice
Implementing scalable, privacy-safe caller discovery requires a principled design that balances performance with safeguards. The approach emphasizes privacy preserving techniques within a scalable architecture, enabling efficient data fusion across sources while minimizing exposure. Validation metrics quantify latency, accuracy, and robustness. Empirical results guide optimization, revealing tradeoffs between throughput and privacy guarantees, and ensuring transparent, auditable processes for freedom-focused stakeholders.
Conclusion
This study presents a disciplined view of reliable caller discovery, favoring measured improvements over grandiose claims. By framing signals as complementary rather than definitive, the approach reframes uncertainty into actionable insights. The data-driven narrative emphasizes transparent performance metrics, auditable processes, and privacy safeguards as guardrails, rather than constraints. In this context, progress is depicted as incremental reliability gains, with cross-layer validation guiding cautious optimism and stakeholder trust through demonstrated, repeatable outcomes.





