Digital Record Inspection – 070005043c160permanente, cabtipc2a, fm24451mr3, @unatalvale4, 001000p05461
Digital Record Inspection for 070005043c160permanente, cabtipc2a, fm24451mr3, @unatalvale4, 001000p05461 is framed as a disciplined evaluation of electronic documents, metadata, and system logs to establish authenticity, integrity, and lifecycle compliance. The discussion centers on provenance, invariant metadata, and chain-of-custody controls, with an emphasis on reproducible methods and independent verification. It stops short of conclusions, inviting scrutiny of steps, evidence quality, and potential anomalies that warrant further examination.
What Digital Record Inspection Is and Why It Matters
Digital record inspection refers to the systematic examination of electronic documents, metadata, and system logs to verify authenticity, integrity, and compliance. It frames processes, controls, and evidence chains that support governance. By evaluating data integrity and metadata provenance, stakeholders discern tampering risks, establish traceable histories, and sustain trust. The approach emphasizes reproducibility, transparency, and rigorous documentation for auditable digital records.
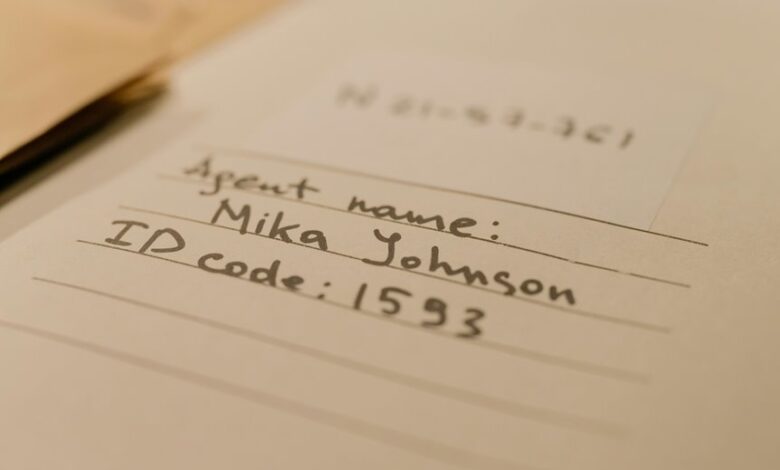
Key Identifiers and Provenance Tracing in Practice
Key identifiers and provenance tracing in practice hinge on delineating unique, tamper-evident markers across the digital record lifecycle. The methodology emphasizes invariant metadata as stable anchors, enabling consistent cross-reference despite transformations.
Provenance management codifies chain of custody, documenting origin, custody events, and integrity checks. This disciplined approach supports accountability, traceability, and resilience against subtle alterations within complex information ecosystems.
Auditing Workflows: Steps to Verify Authenticity and Surface Anomalies
Auditing workflows for authenticity centers on a structured sequence of verification steps that systematically uncover inconsistencies and surface anomalies. The process emphasizes traceable checks, independent cross-verification, and documentation integrity to establish legitimate provenance. Anomaly indicators are evaluated against baselines, revealing deviations in timestamps, lineage gaps, or duplicated artifacts. Precision-focused methodologies minimize subjective interpretation while supporting transparent, audit-ready conclusions.
Building a Repeatable, DEF-Compliant Inspection Routine
A repeatable, DEF-Com-compliant inspection routine builds on established verification methods by codifying procedures that yield consistent results across diverse scenarios. The approach emphasizes data integrity and documented chain of custody, ensuring traceability and reproducibility. Standards-driven templates enable objective assessments, while independent validation and periodic updates preserve relevance. Detachment supports rigorous, unambiguous findings, aligning operational freedom with disciplined, verifiable best practices.
Frequently Asked Questions
How Do I Handle Missing Metadata During Inspections?
Handling metadata requires preserving context through robust preservation strategies, auditing workflows, and schema evolution; forensic tagging and format migration reinforce integrity policies and codec resilience, while continuous evaluation ensures metadata accuracy, enabling resilient, auditable digital record preservation.
What Are Common False Positives in Record Integrity Checks?
False positives commonly arise from benign timestamp drift, checksum collisions, and non-standard encodings, complicating record integrity assessments. Meticulous verification, cross-referencing metadata, and reproducible checks are essential to distinguish genuine discrepancies from innocuous aberrations in analytical workflows.
Can Inspections Adapt to Evolving Digital Formats and Codecs?
Inspections can adapt to evolving formats and codec adaptation, provided metadata and validation rules are updated accordingly; a framework supporting modular decoders and format inventories enables ongoing compatibility, ensuring rigorous scrutiny while preserving analytical freedom for researchers.
Which Tools Support Offline, Secure Verification Workflows?
Offline verification and secure workflows are supported by established tools like OpenTimestamps, Bridges, and PGP-based solutions, enabling independent validation, tamper resistance, and auditable records; parallel processes ensure reliability, reproducibility, and freedom in digital preservation.
How Is User Access History Audited for Compliance?
Audit trails capture user access events, timestamps, and actor identities to support data governance and compliance. They enable verification, anomaly detection, and accountability, balancing transparency with privacy while preserving system freedom and operational integrity. Access control, immutable logging.
Conclusion
In sum, digital record inspection affords rigorous verification of authenticity, integrity, and lifecycle compliance through disciplined provenance tracing and invariant metadata analysis. Systematic auditing workflows reveal anomalies with reproducible methods, while independent verification enforces objective credibility. The procedure establishes a defensible chain of custody and auditable evidence, ensuring consistent outcomes across environments. Its precision is so exacting that it can feel like mapping every photon’s echo—an astronomical standard for trust in digital records.





