Identifier Accuracy Scan – 6464158221, 9133120993, Vmflqldk, 9094067513, etnj07836

Identifier Accuracy Scan raises questions about how distinct identifiers—6464158221, 9133120993, Vmflqldk, 9094067513, etnj07836—align with their intended entities across systems. The approach is methodical: validate formats, apply checksums, and assess probabilistic matches to detect noise or spoofing. Governance and auditable logs govern decisions, balancing false positives with integrity. The outcome hinges on reproducible rules and clear remediation paths, but the path forward remains nuanced and requires careful scrutiny. What specific failures and fixes will surface as alignment is tested?
What Is Identifier Accuracy and Why It Matters
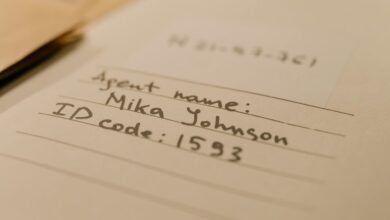
Identifier accuracy refers to the alignment between any given identifier and the specific entity it is intended to denote, ensuring that each code, number, or token maps unequivocally to its correct subject. This meticulous alignment preserves data integrity across systems, enabling reliable cross-referencing, auditability, and operational trust.
In practice, standardized identifiers reduce ambiguity, facilitate interoperability, and uphold consistent decision-making within complex information environments.
How Noise, Spoofing, and Cross-System Reconciliation Break Identities
Noise, spoofing, and cross-system reconciliation introduce distinct pressures that can destabilize identifier integrity across networks.
The discussion proceeds with measured analysis of interference sources, their propagation paths, and containment strategies.
It describes how noise and spoofing distort signals, how mismatched cross system reconciliation creates gaps, and how structured auditing reveals inconsistencies, enabling targeted remediation without compromising operational autonomy.
Techniques to Validate and Match Identifiers (Checksum, Formats, Probabilistic Matching)
To validate and match identifiers effectively, practitioners implement a layered approach that combines checksum algorithms, standardized formats, and probabilistic matching to assess consistency across data sets. The method emphasizes reproducibility, traceable decision rules, and verifiable audits. It acknowledges privacy risk considerations, aligns with data governance requirements, and seeks balanced tolerance for false positives while preserving operational freedom and analytical integrity.
Building a Practical Identifier Scan Blueprint (Best Practices, Pitfalls, and Real-World Use Cases)
A practical identifier scan blueprint integrates structured workflows, validation rules, and governance controls to enable reliable detection, reconciliation, and remediation across disparate data sources. It emphasizes repeatable procedures, explicit ownership, and auditable logs.
Attention to identity misalignment and data authenticity guides risk assessment, tooling choices, and real-world use cases, while avoiding overreach, ensuring clarity, and supporting scalable, autonomous operation in diverse environments.
Frequently Asked Questions
How Are Identifiers Protected From Quantum-Era Threats Today?
Identifiers are protected through layered cryptographic standards, post-quantum readiness, and rigorous lifecycle controls, ensuring resilience against advances. Practitioners assess quantum risks, implement quantum-safe algorithms, rotate keys, and enforce least-privilege access with continuous monitoring and auditing.
Can Biometric Traits Collide With Numeric Identifiers in Mixtures?
Biometric collisions can coexist with numeric identifiers, but careful identifier reconciliation is required to separate modalities; cross-checking traits, probabilistic matching, and layered assurance mitigate ambiguity while preserving individual autonomy and system resilience against fraud.
What Is the Cost Impact of Large-Scale Identifier Audits?
The cost impact of large scale identifier audits centers on implementation, data governance, and compliance. It quantifies resource demands, process overhead, and risk reduction; precise budgeting depends on scope, frequency, tooling maturity, and organizational readiness for change.
How Do Legal Constraints Affect Cross-Border Identifier Reconciliation?
Could legal constraints limit cross-border biometric collisions when reconciling identifiers? The detached analyst notes legal constraints shape processes, requiring region-specific compliance, data minimization, and interoperable standards, ensuring cross border identification remains accurate while balancing privacy and operational feasibility.
Which Industries Face the Greatest Interoperability Challenges?
Finance, healthcare, and manufacturing face the greatest interoperability challenges, driven by complex data governance requirements and opaque data lineage. Cross-domain standards gaps hamper reconciliation, demanding rigorous methodologies to maintain accurate identifiers and transparent lineage while preserving data freedom.
Conclusion
The identifier accuracy scan delivers a disciplined framework for cross-system mapping, emphasizing reproducible rules, auditable logs, and governance alignment. By layering checksums, standardized formats, and probabilistic matching, it mitigates noise and spoofing while preserving data integrity. Practitioners should expect disciplined remediation workflows and clear accountability trails, enabling reliable reconciliation across sources. Like a meticulous librarian aligning shelved volumes, the approach ensures each identifier aligns with its intended entity, sustaining trust and operational clarity.