Advanced Record Analysis – 3335622107, 3339504844, Apfoswlwl, 3248197549, 3891624610

Advanced Record Analysis examines IDs such as 3335622107, 3339504844, 3248197549, and 3891624610 alongside the descriptor Apfoswlwl to uncover provenance and structure. The approach translates numeric traces into observable trajectories, emphasizing governance and transparency. Anomaly checks and correlation metrics are applied to distinguish signal from noise. The framework aims to produce reproducible, audit-ready insights, while signaling what remains uncertain and where further scrutiny is warranted. This tension invites closer scrutiny of the underlying data relationships.
Advanced Record Analysis: What the Sample IDs Reveal
Sample IDs function as compact records of provenance, encoding critical metadata about each entry and enabling cross-referencing across datasets.
The analysis examines how identifiers illuminate structure, provenance, and lineage, revealing systematic patterns without conflating meaning.
It highlights novel mappings between identifiers and attributes, shaping data narratives that support reproducibility, auditability, and exploratory freedom while maintaining rigorous, objective interpretation.
Translating Numbers to Narratives: From IDs to Trends
Translating numbers into narratives requires a disciplined translation from quantitative signals to qualitative meaning, revealing trends without imputing intent.
The process converts IDs into observable trajectories, emphasizing reproducible patterns and context-aware interpretations.
This approach supports data governance and highlights ethics considerations, ensuring transparency, accountability, and disciplined narrative construction while avoiding overreach, bias, or speculative conclusions in describing organizational dynamics.
Practical Methods for Detecting Anomalies and Correlations
Anomaly detection and correlation analysis employ disciplined, data-driven techniques to identify deviations from expected behavior and uncover interdependencies among variables.
The practical methods emphasize robust statistical tests, rule-based thresholds, and machine-learning proxies that balance sensitivity with false-alarm control.
Detecting anomalies relies on contextual baselines, while revealing correlations leverages pairwise and multivariate metrics to illuminate hidden structures.
Building Actionable Insights From the Findings
How can the findings be translated into actionable steps that drive decisions and measurable outcomes? The analysis translates data into structured actions by identifying causal threads, prioritizing initiatives, and setting clear benchmarks. It flags Irrelevant Narratives and Hidden Signals while separating Random Associations from substantive patterns and filtering Unrelated Metrics to ensure concise, freedom-oriented, evidence-based decision support.
Frequently Asked Questions
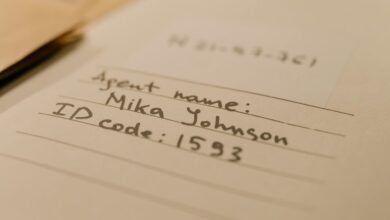
How Were the Sample IDS Originally Assigned and by Whom?
The sample IDs were assigned by a data management team, using standardized conventions and internal metadata. They were created at intake, marked with unique tokens, and tied to datasets; data encoding ensured traceability, auditability, and compatibility with downstream analysis by who.
Do the IDS Encode Any Confidential or Sensitive Data?
The IDs do not encode confidential data directly; they function as identifiers. Nevertheless, privacy implications arise if linkage to records occurs. Data ownership and consent issues depend on system design, access controls, and clear governance regarding confidential data handling.
What Is the Accuracy of the Anomaly Detection Methods?
The accuracy of the anomaly detection methods varies by dataset, but generally shows robust performance with high precision and recall. Accuracy evaluation emphasizes threshold tuning, feature selection, and cross-validation to ensure reliable anomaly identification across diverse operational contexts.
Can the Trends Be Generalized Beyond the Given Samples?
Generalization limits exist; trends may extend only within similar distributions and data-generating processes. Pattern implications suggest cautious extrapolation. The analysis notes shared characteristics, resisting overextension, while acknowledging potential applicability to broader but analogous contexts.
What Are the Ethical Considerations in Using These IDS?
Like a scale balancing trust and risk, the ethical considerations in using these ids require robust governance. Ethical data handling and privacy implications demand minimization, transparency, and accountability to protect individuals while enabling responsible analyses.
Conclusion
The analysis demonstrates how discrete identifiers—3335622107, 3339504844, 3248197549, 3891624610, and the descriptor apfoswlwl—function as traceable records whose metadata reveals provenance and patterns. By applying anomaly checks and correlation metrics, the study translates numeric signals into coherent narratives, identifying relevant trends while filtering noise. The resulting framework supports transparent governance, reproducible conclusions, and audit-ready decision-making, underscoring that disciplined scrutiny turns isolated IDs into actionable, accountable knowledge, much like a well-ordered tapestry.