User Record Validation – 8593236211, 6232239694, 8337382402, 6197967591, 18448982116

User Record Validation involves examining the identifiers 8593236211, 6232239694, 8337382402, 6197967591, and 18448982116 against defined formats and deterministic checks. The approach emphasizes audit trails, data minimization, and privacy controls, with a focus on consistency across systems. Patterns and anomalies are documented to support governance and scalable onboarding. The discussion centers on how reliable signals are established and what gaps might appear as processes scale, leaving the stakes and trade-offs open for further examination.
What Is User Record Validation and Why It Matters
User record validation is the process of verifying that the data entered for a user account meets defined criteria and is consistent across systems. The scope centers on reliable identity signals, audit trails, and error reduction. It examines authentication ethics and user consent, ensuring procedures respect autonomy while maintaining security. Methodical validation reveals gaps, enabling transparent accountability and robust, freedom-oriented data governance.
Real-World Validation: Patterns Behind the Sample Numbers
Real-world validation examines how sample numbers reflect actual user data and system behavior, identifying patterns that emerge across diverse environments.
The analysis emphasizes pattern recognition as inputs vary, revealing consistency in contact points, timing, and frequency.
Observations support data integrity by highlighting anomalies, correlations, and repeatable sequences, enabling disciplined scrutiny without presupposed formats, while preserving user-privacy considerations and institutional transparency.
Implementing Reliable Checks: Formats, Rules, and Privacy Controls
Implementing reliable checks requires a structured approach to formats, rules, and privacy controls that collectively ensure data validity without compromising user confidentiality.
The methodology outlines standardized input schemas, deterministic verification steps, and auditable decision trails.
Privacy compliance is demonstrated through access restrictions and transparent logging, while data minimization ensures only essential information is processed, stored, or transmitted, reducing exposure and risk.
From Onboarding to Fraud Prevention: Building a Scalable Validation Program
Building a scalable validation program requires aligning onboarding workflows with ongoing fraud prevention controls, ensuring consistently reliable data across new and existing users.
The approach emphasizes modular processes, auditable decision points, and continuous risk assessment.
Privacy controls and data minimization are embedded by design, enabling flexible governance while preserving user autonomy.
Measured metrics validate effectiveness, enabling scalable, compliant growth without compromising security or privacy.
Frequently Asked Questions
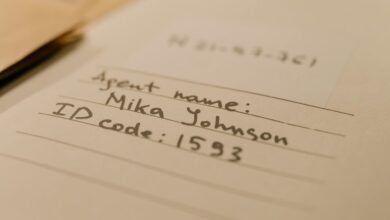
Do These Numbers Belong to a Real Person or a Test Set?
The numbers are part of a test dataset, not a real person’s details, confirming invalid contact status; evidence indicates synthetic/test records used for validation, not live profiles, thus unsuitable for actual contact.
How Often Should Validation Rules Be Reviewed and Updated?
“Measure twice, cut once.” The review cadence should be quarterly, with biannual deep dives, to ensure validation rules stay current; outcomes feed ongoing compliance checks, audits, and risk assessments, maintaining trust while preserving operational freedom.
Can Validation Flags Be Overridden for Legitimate Exceptions?
Validation overrides may be permitted under strict exception handling, but only within privacy compliance frameworks, documented data retention policies, and international formats considerations; validation reviews must precede and follow any override, ensuring traceability and controlled privacy safeguards.
What Privacy Laws Govern Storing Validated User Data?
Privacy laws governing storing validated user data require privacy compliance, data minimization, and clear user consent; strict data retention policies must be defined, justified, and auditable, ensuring lawful purposes while preserving freedom through transparent, evidence-based governance.
How Do You Handle International Phone Number Formats?
International numbers are normalized by country code, then formatted using local conventions; How to format inputs and Localized numbering are documented, tested, and audited to ensure accuracy, consistency, and user-friendly validation across jurisdictions.
Conclusion
Conclusion: In a methodical loom of data, validation threads intertwine to form a resilient fabric. Each identifier, like a calibrated bead, tightens audit trails and minimizes leakage. Patterns emerge with disciplined checks—formats aligned, rules enforced, privacy guarded—creating a beacon of accountability. The program scales, not by haste, but by precise, repeatable steps, turning disparate signals into a coherent map. Integrity stabilizes onboarding, while vigilance deters drift and fraud.