Digital Record Inspection – 18002251115, 3205678419, 16193590489, 18009320783, 18779991956

Digital Record Inspection applies methodical scrutiny to digital artifacts, treating markers such as 18002251115, 3205678419, 16193590489, 18009320783, and 18779991956 as potential provenance indicators. The approach is disciplined: verify, cross-check, and document findings with reproducible steps. The aim is transparent accountability, linking logs, metadata, and network traces to origin and integrity. The question remains what hidden connections these identifiers reveal, and what deviations might imply about the trace’s reliability.
What Digital Record Inspection Really Is and Why It Matters
Digital record inspection refers to the systematic examination of digital artifacts—such as files, metadata, system logs, and network traces—to uncover factual state, provenance, and integrity of information.
In this context, digital forensics provides methodical techniques for evidence gathering, while data provenance clarifies source lineage and transformations.
The practice is proactive, analytical, and freedom-facing, enabling reliable accountability, decision-making, and resilient information governance across complex digital environments.
Decoding the Numbers: What 18002251115, 3205678419, 16193590489, 18009320783, 18779991956 Represent
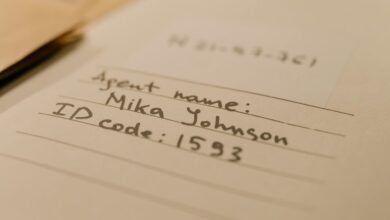
In the wake of establishing how digital records are examined for provenance and integrity, the focus shifts to interpreting numeric identifiers that frequently surface in logs and metadata. The listed numbers are not arbitrary strings but potential markers, timestamps, or hashes.
Decoding numbers requires methodical checks for encoding schemes, while recognizing cryptic meanings may reveal provenance, integrity, or process steps behind each entry.
A Practical Guide to Inspecting Digital Trails Step by Step
How can investigators systematically uncover the provenance and reliability of digital trails, and what steps ensure each indicator is evaluated with rigor? The guide outlines a disciplined sequence: map indicators, document origin, apply verification methods, assess integrity, and log deviations. It highlights insight gaps and confirms correlations without bias, enabling precise judgments while preserving investigative freedom and methodological rigor.
Pitfalls, Tools, and Best Practices for Reliable Record Verification
Pitfalls, Tools, and Best Practices for Reliable Record Verification require a disciplined inventory of common failure modes, appropriate instrumentation, and standardized workflows. The analysis identifies systematic risks, distinguishes human and technical toils, and emphasizes transparent provenance. Practical frameworks prioritize validated tools, rigorous cross-checks, and reproducible methods. Pitfalls toils, tools pitfalls are mapped to mitigations, cultivating disciplined, freedom-friendly verification that remains concise, traceable, and objective.
Frequently Asked Questions
What Are Common Myths About Digital Record Inspection?
Common myths about digital record inspection include overestimating invasiveness, underestimating governance, and assuming immediate results; these myths fuel audit misconceptions. The analysis emphasizes myth busting, proactive controls, and freedom through transparent, meticulous, data-driven decision-making.
How Can Privacy Concerns Be Addressed During Audits?
Audits address privacy concerns by implementing rigorous privacy safeguards and maintaining audit transparency; data minimization and access controls reduce exposure, while clear reporting and independent reviews ensure accountability, enabling stakeholders to pursue freedom with confidence in protective measures.
Which Hidden Costs Appear in Long-Term Record Verification?
Hidden costs emerge from long term verification, including ongoing storage, archival integrity checks, and compliance audits. The approach is analytical, meticulous, and proactive, enabling a freer audience to foresee expenses, plan budgets, and minimize unforeseen financial burdens.
Do Digits Like 18002251115 Indicate Device Origin?
The digits do not reliably indicate device origin; no single numeric pattern guarantees provenance. origin digits and device provenance remain inferential, requiring corroborating metadata and logging analyses to support claims about source, ownership, and chain of custody.
How to Handle Incomplete Data During Verification?
Patience pays off; a stitch in time saves nine. Incomplete verification is managed by documenting data gaps, triangulating with corroborating sources, and outlining remediation steps, enabling rigorous analysis despite incomplete verification and preserving overall data integrity.
Conclusion
In a steady, third-person cadence, the investigation closes with guarded clarity. The数字 markers, like quiet keystrokes in a vast archive, yield testament to provenance when cross-checked against logs and network traces. Each finding is mapped, verified, and documented with disciplined precision, revealing a transparent chain of custody. The conclusion remains proactive: anomalies are logged, interventions cataloged, and reproducible steps preserved, ensuring future inquiries echo the same measured rigor and enduring accountability.