Technical Entry Check – Sshaylarosee, 3348310681, Htlbvfu, 3801979997, 9132976760

Technical Entry Check establishes a structured verification step for data labeled Sshaylarosee, 3348310681, Htlbvfu, 3801979997, and 9132976760. The approach emphasizes accuracy, completeness, and traceability before broader system entry. It maps identifiers to defined roles, supporting governance and auditable logs. The framework enables independent checks and modular procedures, aligning onboarding, risk, and compliance. A disciplined process reduces ambiguity, yet introduces questions about scope and exceptions that warrant careful continuation.
What Is a Technical Entry Check and Why It Matters
A technical entry check is a structured verification process used to confirm the accuracy and completeness of technical data before it enters a broader system or workflow. It assesses data quality, traceability, and consistency, supporting entry integrity.
With formalized roles and controls, verification governance ensures accountability, reduces risk, and enables transparent decision-making while preserving freedom to innovate within well-defined standards.
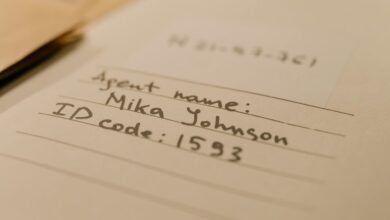
Decoding the Identifiers: Sshaylarosee, 3348310681, Htlbvfu, 3801979997, 9132976760
Decoding the Identifiers: Sshaylarosee, 3348310681, Htlbvfu, 3801979997, 9132976760 involves mapping each label to its role within the technical entry framework, clarifying how unique identifiers support data traceability and integrity.
The process frames Onboarding risk within a structured Compliance framework, aligning records, access, and audits, while preserving autonomy and transparency for stakeholders seeking freedom through accountability.
A Practical Framework for Onboarding, Risk Assessment, and Compliance
A practical framework for onboarding, risk assessment, and compliance integrates structured processes that align new participant intake with ongoing governance. The onboarding framework emphasizes transparent criteria, documented roles, and auditable steps. Risk assessment identifies threats, assigns ownership, and informs controls. This approach sustains freedom by reducing ambiguity while preserving accountability, enabling scalable, compliant growth without unnecessary bureaucracy or friction.
Best Practices to Implement Robust, Traceable Entry Verification
Best practices for robust, traceable entry verification emphasize systematic controls and observable evidence. The approach favors modular procedures, auditable logs, and independent checks to reduce ambiguity. Documentation clarifies responsibilities and milestones, enabling timely exception handling. Discussion ideas: onboarding risks, compliance traceability. Transparent governance supports freedom by ensuring accountability without constraining initiative, while continuous improvement sustains resilience through measurable performance indicators and consistent verification across processes.
Frequently Asked Questions
How Is Data Privacy Protected During Entry Checks?
Data privacy during entry checks is maintained through stringent access control and data integrity practices, ensuring only authorized personnel access sensitive information while maintaining verifiable records and minimal data exposure, promoting freedom with responsible stewardship and auditable safeguards.
Who Audits the Entry Verification Process?
Auditors are independent internal and external bodies, ensuring accountability. Idea one, shareability constraints, govern documentation access; Idea two, cross department ownership, oversees verification accuracy. The system remains transparent, auditable, and balanced between security needs and freedom of information.
What Are Typical False-Positive Indicators?
Metaphorically, false positives arise when signals mislead; indicators include elevated noise, unstable thresholds, and inconsistent labeling. Data drift can exacerbate errors, causing misclassification and delayed detection, though continuous monitoring seeks calibration, reducing false positives over time.
How Often Are Identifiers Refreshed or Rotated?
Identifiers are refreshed periodically per policy, balancing operational needs and security. Refresh frequency aligns with data retention and access control goals, while breach notification considerations shape rotation cadence; data minimization supports only essential identifier reuse.
Can Entry Checks Be Automated Across Departments?
Entry checks can be automated across departments. The approach leverages automation checks and cross department workflows, enabling consistent enforcement while preserving autonomy. Structured governance ensures visibility, auditable processes, and scalable deployment across diverse teams seeking freedom.
Conclusion
The Technical Entry Check stands as a precise gatekeeper, contrasting complexity with clarity. While identifiers—Sshaylarosee, 3348310681, Htlbvfu, 3801979997, 9132976760—anchor governance, procedures reveal the same goal: accountability through traceable logs. As onboarding streams forward, risk assessments and compliance sharpen, yet independence remains intact. The result is a guarded openness: rigorous controls enabling timely exceptions, and scalable growth enabled by documented milestones. In this juxtaposition, governance and agility converge, ensuring trustworthy entry without sacrificing speed.