Network & Call Validation – Getcarttl, 8448768343, Hjrjyf, Hdpprzo, 3126826110

Network & Call Validation relies on Getcarttl to establish ownership and provenance for numbers such as 8448768343 and 3126826110, linking them to accountable controllers beyond simple routing checks. The approach maps identities to numbers, enabling transparent connections like Hjrjyf and Hdpprzo within a trusted ecosystem. By standardizing validation workflows and monitoring latency, misroutes and fraud can be detected. The discussion invites a closer look at practical workflows and real-world implications that follow this framework.
What Is Network & Call Validation and Why It Matters?
Network and call validation is a verification process used to confirm the authenticity and integrity of telecommunications traffic. It identifies fraudulent or malformed connections, reducing risk and disruption. The practice enhances confidence in communications, enabling safer networks and reliable messaging. Key elements include refusal of suspicious activity, standardized checks, and ongoing monitoring. Network validation and call validation ensure resilient, trusted interchanges across services.
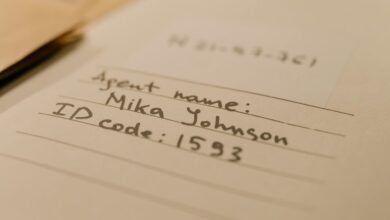
Verifying Ownership: From Numbers to Identities (Getcarttl & Beyond)
Verifying ownership connects the dots between a phone number and its rightful controller, extending beyond basic network checks to establish verifiable identities. The process emphasizes identity mapping, linking numbers to responsible parties. Through rigorous network validation and call validation, stakeholders gain transparent accountability, enabling trust and consent while preserving freedom to pursue legitimate communication with confidence and verifiable provenance.
Ensuring Routing Integrity: Detecting Fraud, Latency, and Misroutes
Ensuring routing integrity requires systematic detection of fraud, latency, and misroutes within communication networks. This analysis emphasizes mechanisms for flagging incorrect routing events and enabling prompt fraud detection. It outlines verification checks, latency benchmarks, and path validation to deter manipulation.
A structured approach aids operators in maintaining consistent routing behavior, promoting transparency, reliability, and trust across interconnected systems.
Build Practical Validation Workflows: Steps, Tools, and Real-World Examples
Practical validation workflows translate abstract concepts into repeatable procedures by detailing the sequence of steps, the tools required, and concrete real‑world examples. This section outlines a disciplined approach: define objectives, map data flows, select validation workflows, implement checks, and document outcomes. Readers explore practical tools, repeatable scenarios, and real deployments, enabling measurable quality improvements and freedom through structured, verifiable processes.
Frequently Asked Questions
How Does Getcarttl Handle Privacy During Verification?
Getcarttl limits exposure through privacy practices and data minimization. It verifies identities while restricting collected data, retaining only essential details, and employing secure handling. The approach emphasizes user autonomy and transparent safeguards, balancing verification needs with individual privacy.
Can Validation Errors Cause Legitimate Numbers to Be Blocked?
Yes, validation errors can mistakenly block legitimate numbers. The system should balance privacy controls and user access, minimizing data collection while ensuring accuracy. Data minimization supports safeguard efficacy; transparent policies help maintain freedom while reducing false positives.
What Are Unseen Costs of Advanced Network Validation Tools?
Unseen costs arise from advanced tools, including privacy handling, verification workflows, carriers scalability, and real time validation. User consent and identity workflows add complexity, while deployment and maintenance pressures demand resources for ongoing privacy compliance and governance.
Do Carriers Support Automated, Real-Time Validation at Scale?
Automated, real-time validation at scale is supported by many carriers, though uptake varies; privacy concerns and data minimization principles guide implementations, balancing throughput with safeguarding personal data while preserving operational freedom and scalable trust in networks.
How Is User Consent Managed in Identity Verification Workflows?
User consent in identity verification workflows is governed by consent governance and privacy safeguards, ensuring transparent collection, revocable permissions, purpose limitation, and auditable records, while preserving user autonomy and enabling compliant, frictionless verification experiences.
Conclusion
Network and call validation, powered by Getcarttl, ties telephone numbers to verifiable identities and ownership, enhancing trust across intercarrier routes. By mapping 8448768343, 3126826110, and linked identifiers like hjrjyf and hdpprzo, networks gain accountability and provenance beyond basic routing checks. An illustrative statistic: organizations implementing standardized validation report up to a 40% reduction in misroutes within the first quarter. This precision-driven approach strengthens transparency, reduces disruption, and supports resilient, verifiable communications ecosystems.